Junho 7, 2024
Digital Fraud
Junho 7, 2024
Enhance Your Database Security with Tracking Tokens
Junho 7, 2024
Ransomware: Protecting Your Clients from One of the Most Severe Digital Threats
Junho 5, 2024
How to Protect Your Brand from Cybersquatting and Typosquatting with a Free Tool
Junho 3, 2024
Automating Incident Response: A Success Story
Junho 3, 2024
2024 Trends for Security Providers: A Comprehensive Guide
Maio 28, 2024
External Threats, Internal Threats, and Digital Risk: What's the Difference?
Maio 21, 2024
How Corporate Credentials Are Sold on the Deep & Dark Web
Maio 21, 2024
What Stealers Can Collect: A Detailed Analysis of the Information
Maio 21, 2024
How to Protect Your Company from Data Exposure and Extortion
Junho 7, 2024
Protecting Access Credentials from Leaks: Essential Solutions for Security Providers
Junho 7, 2024
Enhance Your Database Security with Tracking Tokens
Junho 7, 2024
Ransomware: Protecting Your Clients from One of the Most Severe Digital Threats
Junho 5, 2024
How to Protect Your Brand from Cybersquatting and Typosquatting with a Free Tool
Junho 3, 2024
Automating Incident Response: A Success Story
Junho 3, 2024
2024 Trends for Security Providers: A Comprehensive Guide
Maio 28, 2024
External Threats, Internal Threats, and Digital Risk: What's the Difference?
Maio 21, 2024
How Corporate Credentials Are Sold on the Deep & Dark Web
Maio 21, 2024
What Stealers Can Collect: A Detailed Analysis of the Information
Maio 21, 2024
How to Protect Your Company from Data Exposure and Extortion
Page
1
of 6
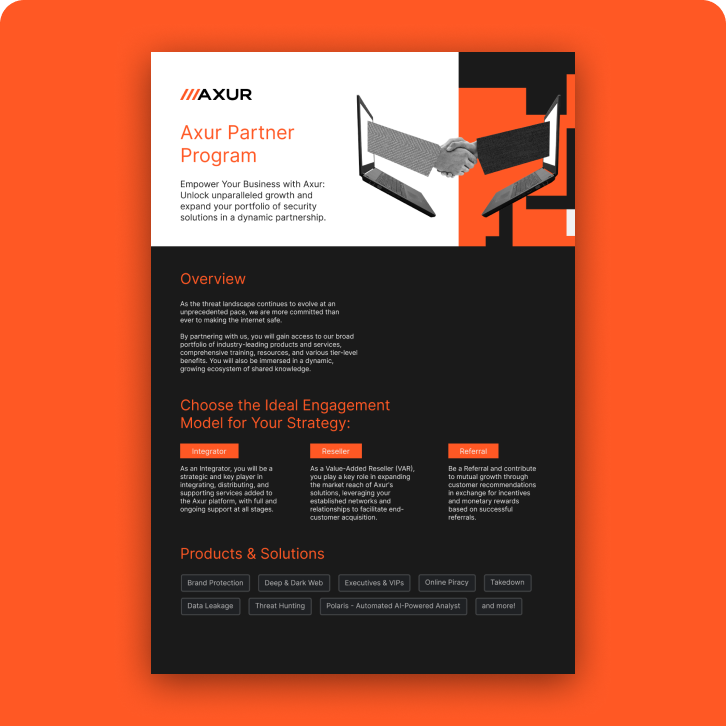
Stay Ahead with Axur Insights
Subscribe to receive the latest cybersecurity content directly in your inbox. Get first-hand access to new resources, updates, and exclusive materials from Axur.